
Losing access to your crypto wallet can mean losing your assets permanently. In 2026, as digital assets continue expanding across exchanges, DeFi platforms, and NFTs, wallet security is the foundation of responsible crypto ownership.
Unlike traditional banking, crypto wallets do not offer automatic fraud reversals. Your private keys are your control — and your responsibility.
This article is for general informational purposes only and does not provide legal, financial, medical, or professional advice. Policies, rates, and regulations may change over time.
What Wallet Security Really Means
Crypto wallet security revolves around protecting one critical element: your private key or seed phrase.
If someone gains access to it, they can:
- Transfer your assets
- Drain your wallet
- Lock you out permanently
For example, entering your seed phrase into a fake “wallet recovery” website immediately exposes your funds to theft.
Security begins with understanding the difference between convenience and protection.
Types of Crypto Wallets and Security Levels
| Wallet Type | Internet Connected | Security Level | Ideal Use |
|---|---|---|---|
| Exchange Wallet | Yes | Moderate | Short-term trading |
| Mobile Wallet | Yes | Moderate | Small balances |
| Desktop Wallet | Yes | Moderate | Active users |
| Hardware Wallet | No | High | Long-term storage |
| Paper Wallet | No | High (if stored properly) | Cold backup |
Hot wallets (connected to the internet) offer convenience but increase exposure. Cold wallets keep keys offline, significantly reducing hacking risk.
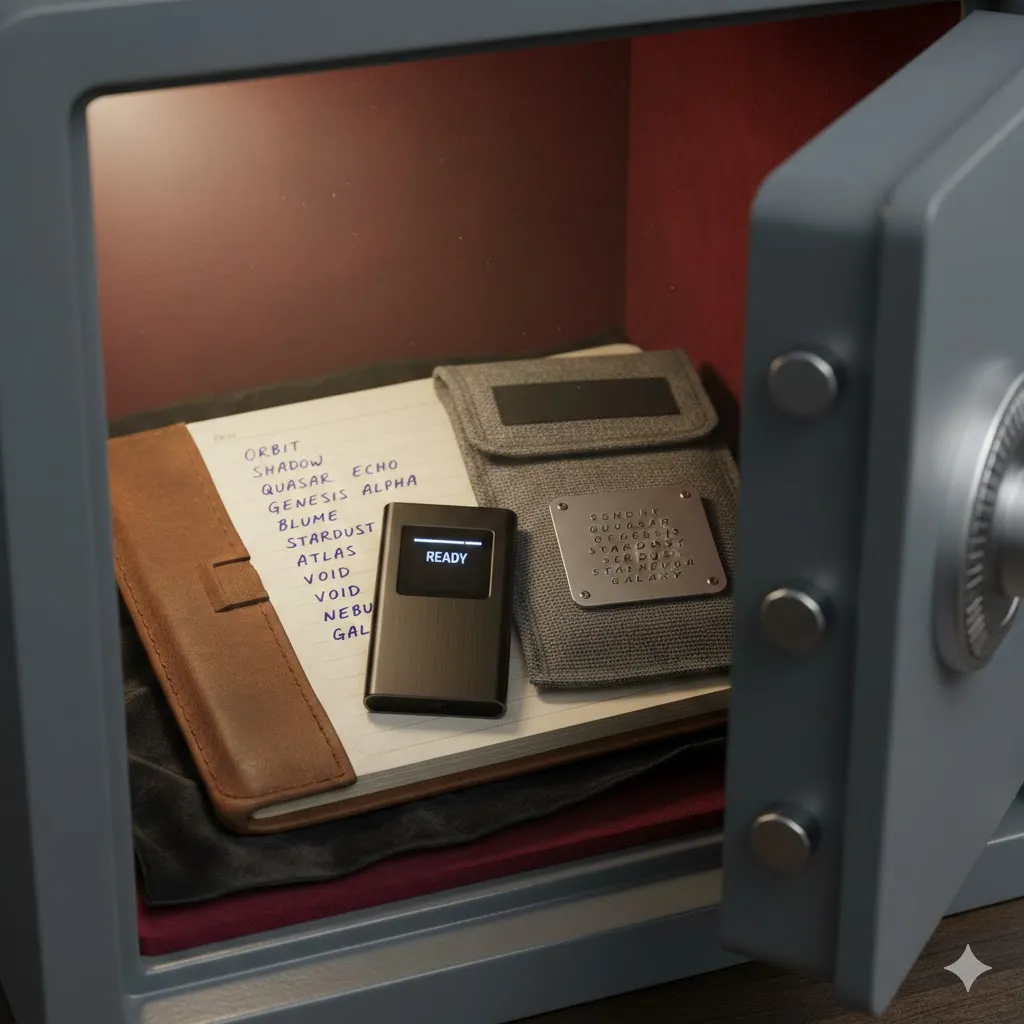
Protect Your Seed Phrase
Your seed phrase is the master key to your wallet.
Best practices:
- Write it down on paper or metal backup
- Store it in a secure physical location
- Never photograph or upload it to cloud storage
- Never share it with anyone
If a website or “support agent” asks for your seed phrase, it is a scam.

Use Strong Authentication
Even secure wallets benefit from layered protection.
Enable App-Based 2FA
Use authenticator apps instead of SMS-based verification to reduce SIM swap risks.
Use Unique Passwords
Never reuse passwords across exchanges or wallets.
Enable Biometric Protection
Fingerprint or facial recognition adds another barrier on supported devices.
Multiple layers reduce single points of failure.
Pro Insight
Most wallet breaches occur through phishing, not technical wallet flaws. Always verify website URLs carefully before logging in or signing transactions.
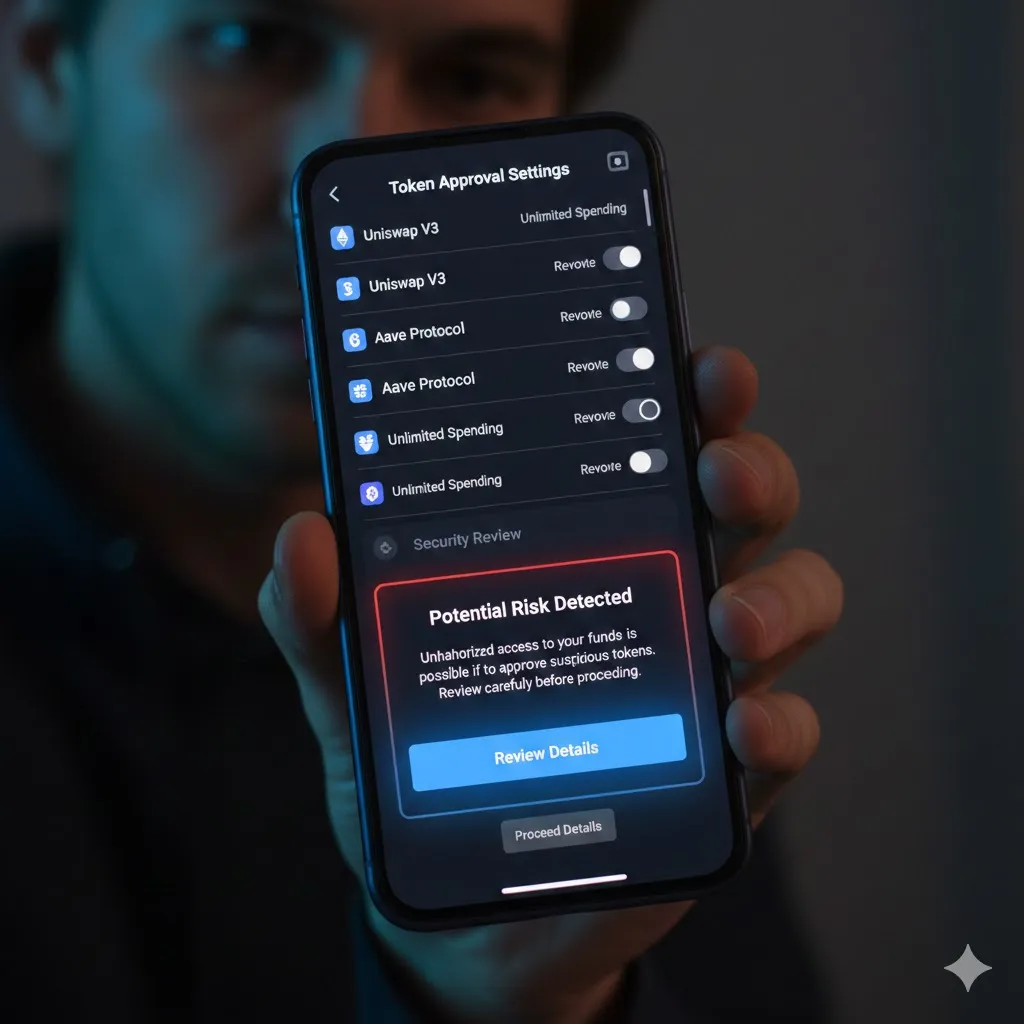
Be Cautious With DeFi and NFT Approvals
When interacting with decentralized applications:
- Review wallet permissions
- Revoke unused token approvals regularly
- Avoid connecting wallet to unknown platforms
Granting unlimited token approval to a malicious smart contract can expose funds without immediate warning.
Avoid Public Wi-Fi for Wallet Access
Public networks increase exposure to:
- Man-in-the-middle attacks
- Malware injection
- Credential interception
If access is necessary, use a trusted VPN and avoid signing transactions.
Backup and Recovery Planning
Losing a device does not mean losing funds — if your backup is secure.
Checklist:
- Store seed phrase securely
- Test wallet recovery process (using small amount first)
- Inform trusted family member about secure storage location (without revealing phrase)
Security also includes disaster preparedness.
Quick Tip
Before confirming any transaction, verify the receiving wallet address character by character. Clipboard malware can silently replace copied addresses.
Frequently Asked Questions
Is a hardware wallet completely safe?
It significantly reduces online risk but still requires secure seed phrase storage.
Should I store crypto on exchanges?
Only small trading amounts. Long-term holdings are generally safer in cold storage.
What is a wallet approval revocation?
It removes smart contract permissions previously granted to access your tokens.
Can I recover funds after sending to wrong address?
Usually not. Blockchain transactions are irreversible once confirmed.
Is SMS 2FA safe?
It is better than no 2FA, but app-based authentication offers stronger protection.
Conclusion
Wallet security in 2026 demands proactive discipline. Protect your seed phrase offline, use hardware wallets for significant holdings, enable strong authentication, and stay alert to phishing threats.
In crypto, control equals responsibility. The more intentional your security practices, the safer your digital assets remain.
Trusted U.S. Resources
U.S. Securities and Exchange Commission (SEC) – Investor Alerts
https://www.sec.gov/
Commodity Futures Trading Commission (CFTC) – Digital Asset Risk Guidance
https://www.cftc.gov/
Cybersecurity & Infrastructure Security Agency (CISA) – Cyber Safety
https://www.cisa.gov/
Federal Trade Commission (FTC) – Cryptocurrency Scam Warnings
https://consumer.ftc.gov/





